Phishing, Vishing, and Smishing, Oh My!
“Lions and tigers and bears, oh my!” Many of you might remember the famed quote Dorothy exclaimed in the Wizard of Oz. You probably also remember the copious perils she and her new friends faced on their quest to get Dorothy back to Kansas. In real life, equally menacing dangers stalk businesses and individuals. Of course, the threats aren’t flying monkeys or green witches. They’re in the form of phishing, vishing, and smishing—oh my!
In today’s connected world, the elusive, unseen bad guys don’t threaten our physical well-being, like Dorothy’s pursuers. Instead, they endanger the data, identities, and livelihoods of individuals and corporations. They do this through cunning, covert techniques designed to trick people into giving up identifying and sensitive personal or company information.
Let’s look at three common methods cybercriminals employ to gain important data from another person or business.
Phishing
Phishing is probably the best-known and most successful attack method. How does it work?
A cybercriminal will send fraudulent emails with malicious attachments or links. The emails are designed to look authentic, often seemingly from an already well-known organization that would elicit trust from the recipient—like a bank, large retailer, or email provider. The emails typically contain an urgency and motivation for the reader to click a link or download an attachment. After clicking, they will be asked to provide sensitive or identifying information, such as login credentials to a bank account, corporate network, or any other account that requires a username and password.
Examples of phishing email language include:
- “Your account is locked. Click here to reset the password.”
- “Your PayPal account has been flagged for fraud. Please verify the attached invoice.”
- “Your email account is full. Click here to clean out old messages.”
Once the unsuspecting recipient provides the requested information, their account or network is compromised. The bad actor now has access. He can use the credentials to log in and steal money, access sensitive data, or conduct any business the valid owner of the account would be able to.
Cybercriminals do their best to create emails that appear legitimate, using copied business logos, expertly designed images, and persuasive language. And they fool many people. But there are ways you can recognize phishing emails and avoid falling into their trap.
Ways to Identify Phishing Emails
- Spelling and grammar errors
- A sense of urgency requiring immediate action
- Included attachments you are not expecting
- Generic salutation, such as “Dear Customer”
- A request for password or account verification
- Sender email domain doesn’t match the organization’s name
- Lack of contact information in the email’s signature
Tips to Avoid Becoming a Victim of Phishing
- Read the email carefully and look closely for all the above items.
- Never click links in an email before first hovering your mouse over the embedded link to see the address. If the URL does not match the company, do not click it.
- Do not open attachments that you are not expecting. If unsure of their validity, contact the sender through a different method—phone, in person, or direct email (not “reply”)—to verify first.
- Employ good password hygiene, meaning do not use the same username and password combination for multiple accounts. Should you accidentally fall victim to a phishing email involving multi-use credentials, all the other accounts for which they are used are also in jeopardy.
 Vishing
Vishing
Vishing criminals have the same motivation as phishing villains, except they use phone calls instead of emails. A recent study revealed that 28% of respondents have received a vishing call. These bad actors use the same scare tactics and urgency, saying things such as:
- “This is the IRS calling about your overdue taxes.”
- “The warranty on your vehicle has expired.”
- “Your account is locked, and we need to verify some information from you to unlock the account.”
Things to Consider When Identifying Vishing Phone Calls
- Is the caller from an institution you know?
- Is the caller trying to scare you into providing information about a legal issue?
- Is the caller trying to sell you something you have not requested?
- Will the caller give you a return phone number so you can call back to verify?
How to Avoid Becoming a Victim of Vishing
- Never give personal information over the phone to an entity that has called you. Always hang up and call the institution directly through a listed phone number to verify the call’s authenticity.
- If someone calls to sell you something you have not requested, do not provide your information.
- Avoid talking with suspected vishing callers as they could potentially record the call and use your voice to authorize other charges or fees.
 Smishing
Smishing
Smishing’s popularity is growing. And as the name suggests, smishing is very similar to both phishing and vishing. The method of delivery for smishing is through SMS messaging (text). Attacks come in the form of a text message that could look like it is either from a person you know, an institute you conduct business with, or an unknown entity. Smishing messages either send a link for you to click so they can then potentially install ransomware, spyware, or other types of nefarious software on your device. And just like phishing emails, smishing texts can send a link that leads to a site intended to steal your personal information.
Characteristics of Smishing Texts
- Messages that request an urgent need for your attention
- Messages from an unknown contact
- Messages that contain attachments or links
How to Avoid Becoming a Victim of Smishing
- Never click links in texts from unknown senders. If you do know them, verify the authenticity if you were not expecting the link.
- Do not open attachments from people you don’t know and scrutinize all attachments from people you do know if you were not expecting them.
- Avoid opening texts from senders that inspire an urgency for you to act, such as, “Your bank account is locked. Click here to gain immediate access.”
Education, Training, and Best Practices
Security training and education are the number one defenses against these attacks. Organizations should provide employees with annual cybersecurity training and documented best practices guidelines—over 32% of employees are prone to phishing attacks. Training should be well rounded, including in-depth phishing, smishing, and vishing content, as well as ransomware and other methods today’s cyber criminals employ. Employers should take heed, as only 28% of respondents feel that they’ve been trained sufficiently in cybersecurity.
Individuals can research online, help educate friends and family, and inform others when they learn of new or evolving threats.
Cyberattacks become more sophisticated and challenging to recognize as criminals hone their craft. Yet even with this evolution, bad actors carry on with standard techniques that continue to hook victims.
To fight back against cybercriminals, learn their methods, stay up to date on new techniques, and remain aware and cautious. The better prepared you are to spot the dangers that cyber criminals pose, the less likely you will fall victim.
Phishing and Vishing and Smishing—No more.
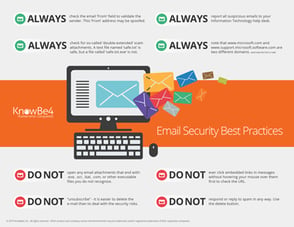 Free Email Security Infographic
Free Email Security Infographic
Print and post around your office, or share electronically with your colleagues. We are all part of the "human firewall."





